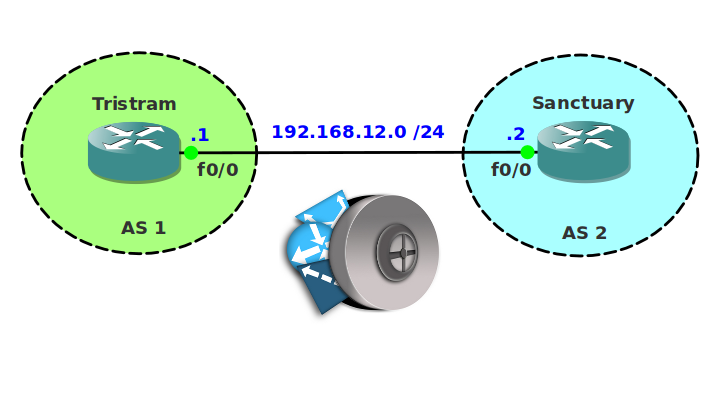
Scenario:
Ever since Diablo was defeated Deckard Cain decided to become a network engineer. Two decades have passed and the village of Tristram has upgraded their network for inter-AS connectivity. Recently some security issues have been reported and Deckard asked you to help him to filter some of the prefixes through BGP. Unfortunately the router does not support prefix-lists so you’ll have to use access-lists to accomplish this.
Goal:
- All IP addresses have been preconfigured for you.
- Configure EBGP between router Tristram and Sanctuary.
- Advertise the loopback interfaces on both routers in BGP.
- Configure a summary that advertises 10.0.0.0/8 towards router Sanctuary.
- Configure an extended access-list on router Sanctuary that will block the 10.0.0.0/8 prefix but allows all other prefixes.
- Configure an extended access-list on router Tristram that blocks network 10.2.2.0/24.
It took me 1000s of hours reading books and doing labs, making mistakes over and over again until I mastered all the routing protocols for CCNP.
Would you like to be a master of routing too? In a short time without having to read 900 page books or google the answers to your questions and browsing through forums?
I collected all my knowledge and created a single ebook for you that has everything you need to know to become a master of routing.
You will learn all the secrets about BGP, access-lists, filtering and more.
Does this sound interesting to you? Take a look here and let me show you how to Master CCNP ROUTE
IOS:
c3640-jk9s-mz.124-16.bin
Topology:
The How to Master series helps you to understand complex topics like spanning-tree, VLANs, trunks, OSPF, EIGRP, BGP and more.
Written by René Molenaar - CCIE #41726


You’re the man. I have never saw a man that uses (in networking) things from transformers, Diablo etc. 😀
thanks 😉 We don’t have to act serious to be serious 😛
Love the naming and all but I’m not seeing the topology file attached. I guessing it’s a work in process. But I’m really looking forward to it.
Still have to fix it…will do so ASAP.
what is the loopback address on the routers?
I just discovered the labs on this site…. This is awesome…Thank you!!! really great for refreshing before the test. I used loopbacks 1.1.1.1 for tristram & 2.2.2.2 for sanctuary; for the ebgp neighborships. and Loopbacks 10.0.0.1/8 & 10.2.2.1/24 for the ACL part.
what IP’s are preconfigured besides the 192
can’t download the topology or solutions for this.
I have my doubts, I need the video an the final configurations, please Rene put them. I want to tell you that I have learned very much with your laboratories, thak so much.
No links for videos.. 🙁
Rene,
Please provide sh run for this lab….m stuck…
Please check and explain me where i have gone wrong…
Tristram#sh run
Building configuration…
Current configuration : 1019 bytes
!
version 12.2
service timestamps debug uptime
service timestamps log uptime
no service password-encryption
!
hostname Tristram
!
!
ip subnet-zero
!
!
no ip domain-lookup
!
ip audit notify log
ip audit po max-events 100
!
call rsvp-sync
!
!
!
!
!
fax interface-type fax-mail
mta receive maximum-recipients 0
!
!
!
interface Loopback0
ip address 1.1.1.1 255.255.255.255
!
interface Loopback1
ip address 10.0.0.1 255.0.0.0
!
interface FastEthernet0/0
ip address 192.168.12.1 255.255.255.0
ip access-group 100 in
duplex auto
speed auto
!
interface FastEthernet0/1
no ip address
shutdown
duplex auto
speed auto
!
router bgp 1
bgp log-neighbor-changes
network 1.1.1.1 mask 255.255.255.255
network 10.0.0.0
aggregate-address 10.0.0.0 255.0.0.0
neighbor 192.168.12.2 remote-as 2
!
ip classless
no ip http server
!
access-list 100 deny ip any 10.2.2.0 0.0.0.255
access-list 100 permit ip any any
!
dial-peer cor custom
!
!
!
!
!
line con 0
exec-timeout 0 0
logging synchronous
line aux 0
line vty 0 4
!
end
Tristram#
———————————————————————————————————————————————————————————————————————————————————-
Sanctuary#term len 0
Sanctuary#sh run
Building configuration…
Current configuration : 1009 bytes
!
version 12.2
service timestamps debug uptime
service timestamps log uptime
no service password-encryption
!
hostname Sanctuary
!
!
ip subnet-zero
!
!
no ip domain-lookup
!
ip audit notify log
ip audit po max-events 100
!
call rsvp-sync
!
!
!
!
!
fax interface-type fax-mail
mta receive maximum-recipients 0
!
!
!
interface Loopback0
ip address 2.2.2.2 255.255.255.255
!
interface Loopback1
ip address 10.2.2.1 255.255.255.0
!
interface FastEthernet0/0
ip address 192.168.12.2 255.255.255.0
ip access-group 100 in
duplex auto
speed auto
!
interface FastEthernet0/1
no ip address
shutdown
duplex auto
speed auto
!
router bgp 2
bgp log-neighbor-changes
network 2.2.2.2 mask 255.255.255.255
network 10.2.2.0 mask 255.255.255.0
neighbor 192.168.12.1 remote-as 1
!
ip classless
no ip http server
!
access-list 100 deny ip any 10.0.0.0 0.255.255.255
access-list 100 permit ip any any
!
dial-peer cor custom
!
!
!
!
!
line con 0
exec-timeout 0 0
logging synchronous
line aux 0
line vty 0 4
!
end
Sanctuary#
I got the answer…
Trinstram,
router bgp 1
bgp log-neighbor-changes
network 1.1.1.1 mask 255.255.255.255
network 10.0.0.0
aggregate-address 10.0.0.0 255.0.0.0
neighbor 192.168.12.2 remote-as 2
neighbor 192.168.12.2 distribute-list 100 in
!
ip classless
no ip http server
!
access-list 100 deny ip 10.2.2.0 0.0.0.255 any
access-list 100 permit ip any any
!
Sanctuary,,,
router bgp 2
bgp log-neighbor-changes
network 2.2.2.2 mask 255.255.255.255
network 10.2.2.0 mask 255.255.255.0
neighbor 192.168.12.1 remote-as 1
neighbor 192.168.12.1 distribute-list 100 in
!
ip classless
no ip http server
!
access-list 100 deny ip 10.0.0.0 0.255.255.255 any
access-list 100 permit ip any any
!
Thanks Rene!!!
Karan, no, you are wrong. Your access-list check only network part of route. The right answer is, for example if 10.0.0.0/8 is variably subnetted, 2 subnets, 2 masks
Extended IP access list 101
10 deny ip host 10.0.0.0 host 255.0.0.0
20 permit ip any any
good lab.
Startup Configuration missing in gns3-old-lab-files for GNS3 version 0.8.6
Please Share it
This was a great little exercise. Really enjoying the site, learning alot about BGP and refreshing things I had forgotten. I have put my other colleges on to this too. thanks alot.
hi there ….
can u please upload the video solution for this lab. cause i really need it for my exam to learn more and to have better degre in my certificate…
best regards
mr.o
I guess, for BGP extended access list format need to be this per the link below.
http://blog.ine.com/2008/01/08/using-extended-acls-for-bgp-filtering/
R2 = Sanctuary
R2#show ip access-lists
Extended IP access list 100
10 deny ip 10.0.0.0 0.255.255.255 255.0.0.0 0.255.255.255 (4 matches)
20 permit ip any any (1 match)