Scenario:
As part of the security team you are always looking for ways to improve security within the company. You want to get rid of all the local vty/console logins within your network so you decide to setup a radius server. Routers should use the external radius server for authentication from now on…let’s see if you can secure this one!
Goal:
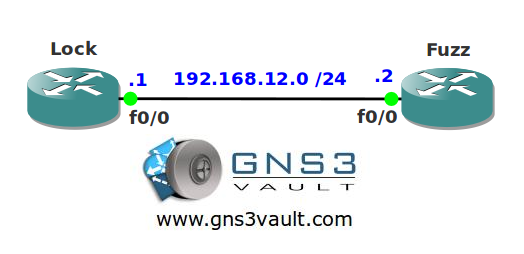
- All IP addresses have been configured for you, look at the topology picture for the IP addresses.
- Configure router Fuzz so it uses the (fictional) radius server at IP address 192.168.23.3. Updates should be sourced from the loopback0 interface.
- Configure router Fuzz so console access uses a local username ‘console’ with password ‘vault’.
- Configure router Fuzz so VTY access uses the radius server, when it fails it should switch to a local username ‘telnet’ with password ‘unsafe’.
- Configure router Fuzz so everyone sees the message “ID required” when they try to login using AAA.
Topology:
 {pub}
{pub}
Configuration Files
You need to register to download the GNS3 topology file. (Registration is free!)Once you are logged in you will find the configuration files right here.
Do you want your CCNA or CCNP Certificate?
The How to Master series helps you to understand complex topics like spanning-tree, VLANs, trunks, OSPF, EIGRP, BGP and more.
Written by René Molenaar - CCIE #41726


I downloaded the zip file but the topology is empty and there are no router configs?
topology is empty
Sorry for that I’ll fix it soon.
there is no tutorial video in many parts of security.
please prepare these files.
thank you
I Agree… many interesting and important videos without solutions…
Hi bro, could you help me out with this here?
Lab requirements states to create two username and password, one for console and one for telnet. Easy.
Problem is, do I have to restrict each to only the line it is authenticating? From my understanding, all the username passwords go into the "local" pool, and we can configure telnet to use radius and fall back to radius. However, are we able to define different local pools such that one pool is for telnet and one pool is for console?
can you take the time for the video answer and the topology file, tanhk you
Topology is empty… no configs….
Rene hello, let me know when you upload the video with the solution for this lab.
pla add some video on security
aaa new-model
aaa authentication banner ^C ID Required ^C
aaa authentication login CONSOLE local
aaa authentication login VTY group radius local
aaa authentication enable default group radius
line con 0
login authentication CONSOLE
line vty 0 4
login authentication VTY
username console password 0 vault
username telnet password 0 unsafe
ip radius source-interface loopback 0